
March 26, 2025
Before you start
This learning module is part of the building block:
The module in brief
In this module, we explore standards and their applications, presenting two standards specifically related to IoT cybersecurity. They are relevant for manufacturers who need to specify product requirements, formalise development processes and document quality in a structured manner. They are also relevant for purchasers of products who need a basis for understanding how to set requirements for products and components in specific solutions.
What is a standard?
A standard is an agreed way of doing something that has been accepted by a group, organisation, or industry. Standards can be technical specifications, guidelines or criteria that aim to ensure that products, services and systems are safe, reliable and function as expected. They help ensure compatibility and quality across different suppliers and markets. The ‘acceptance’ of a standard is highly dependent on the standardisation organisation that authored it. Typically, there is a defined procedure involving consultations and comments from relevant authorities, interest organisation and other experts in the field.
When we talk about standards within Europe/EU, we usually mean the so-called European Standardisation Organisations (ESOs) which are CEN, CENELEC and ETSI. CEN oversees the general systems for standardisation work and ‘common’ standards, CENELEC develops standards for electrical and electronic systems, and ETSI develops standards within telecommunications equipment.
International standardisation organisations include for example ISO and IEC. They can be seen as international counterparts to CEN and CENELEC in relation to their focus areas. In addition, there are national standardisation bodies, such as Dansk Standard, which ensures that Danish interests are also safeguarded in the context of EU standardisation.
Harmonised standards
In the EU, we have the so-called Harmonised Standards. These are standards commissioned by the EU Commission to ensure compliance with specific legislation. They are formulated by one or more European Standardisation Organisations (ESOs) based on a standardisation request from the Commission. Often, these harmonised standards can serve as evidence that a product meets the essential requirements set by the relevant legislation for the product (presumption of conformity), thereby ensuring that the product meets the required quality and safety standards. This means that a manufacturer who has applied the correct harmonised standards for relevant essential requirements of a product can presume conformity to the essential requirements of the relevant legislation.
ETSI EN 303 645
Cybersecurity for consumer IoT: baseline requirements
The EN 303 645A standard is an excellent starting point when it comes to working with standards for IoT cybersecurity. It is one of the easiest standards to deal with, and there are no high expectations regarding technical or organisational measures already in place. The focus area of the standard is consumer IoT and how to address challenges around a basic level of security. This is realised through a series of specific requirements that must be implemented. Some apply to the product, others to the manufacturer's organisation.
Scope of the standard:
-
- Connected children’s toys and baby monitors
- Connected smoke detectors, door locks and window sensors
- IoT gateways, base stations and hubs that multiple devices connect to
- Smart cameras, smart speakers and smart TVs, incl. remote controls
- Wearable health trackers
- Connected home automation and alarm systems, incl. their gateways and hubs
- Connected appliances, such as washing machines and refrigerators
- Smart home assistants
The standard can be downloaded for free here.
General requirements
The standard sets out the following 13 requirements:
-
- Avoid universal default passwords
- Implement a method to manage vulnerability reports
- Keep software updated
- Store sensitive security parameters securely
- Communicate securely
- Minimise exposed attack surfaces
- Maintain software integrity
- Ensure personal data is secure
- Make systems resilient to failures/outages
- Analyse system telemetry data
- Make it easy for users to delete user data
- Make installation and maintenance of devices easy
- Validate input data
Under each of these requirements, there are one or more sub-requirements, which do not necessarily need to be applied to all products. These requirements should be implemented based on a risk analysis for the product. The standard does not set high demands or expectations for the reader and contains plenty of examples of what each individual requirement entails, and what is expected in terms of implementation in the product. For further guidance, please refer to ETSI TR 103 621. Note, however, that it is written for an older version of EN 303 645, so reference discrepancies may occur.
To provide an overview of what has been implemented and on what basis, the standard includes an 'Implementation Conformance Statement' (ICS) in Annex B, where it must be justified why a recommended requirement has not been implemented, with reference to the risk analysis for the product.
Based on the ICS, ETSI TS 103 701 can be used to develop a test plan that form the basis for conducting a conformity assessment of the product against the standard. This can be done internally in an R&D department or outsourced to a third-party facility.
IEC 62443
If you want to advance beyond EN 303 645, you can focus on the IEC 62443 series. This series of standards offers a more comprehensive approach by defining a set of development and maintenance processes that must be managed.
This series of standards addresses cybersecurity for industrial automation and control systems and includes a number of different standards, as shown in the overview below.
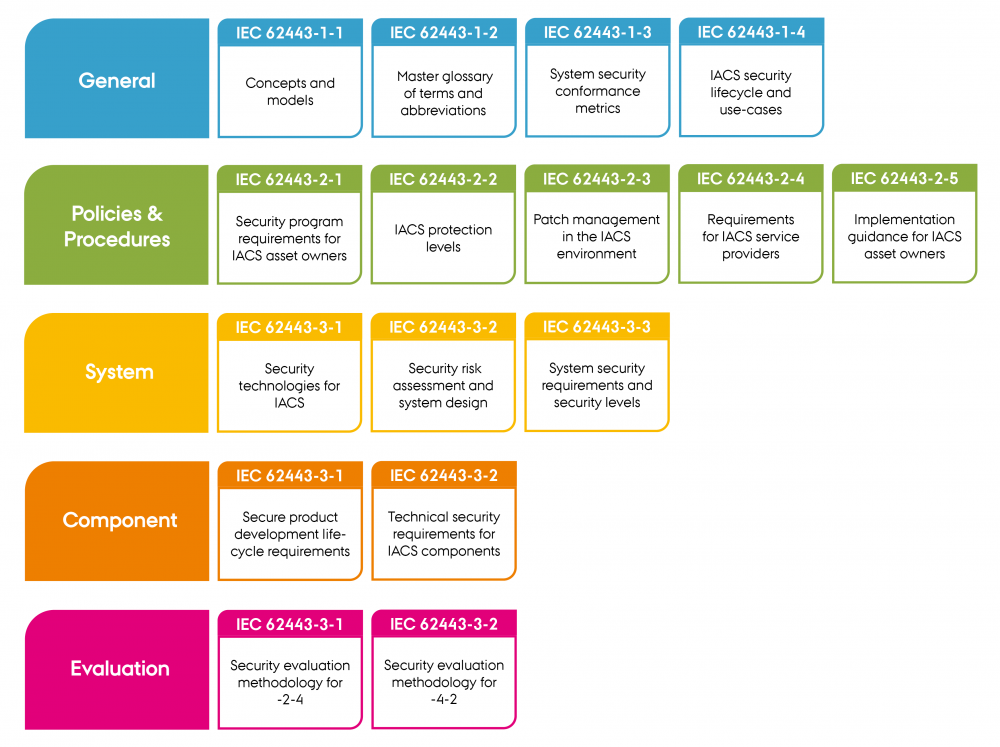
"Standards within the IEC 62443 series" by CyPro under license CC BY-SA 4.0
![]()
Standards within the IEC 62443 series
Printable version of the tool in large format
These standards encompass far more than product development. They also address e.g. how to manage suppliers and ownership of assets. The interplay between the many standards is shown here:
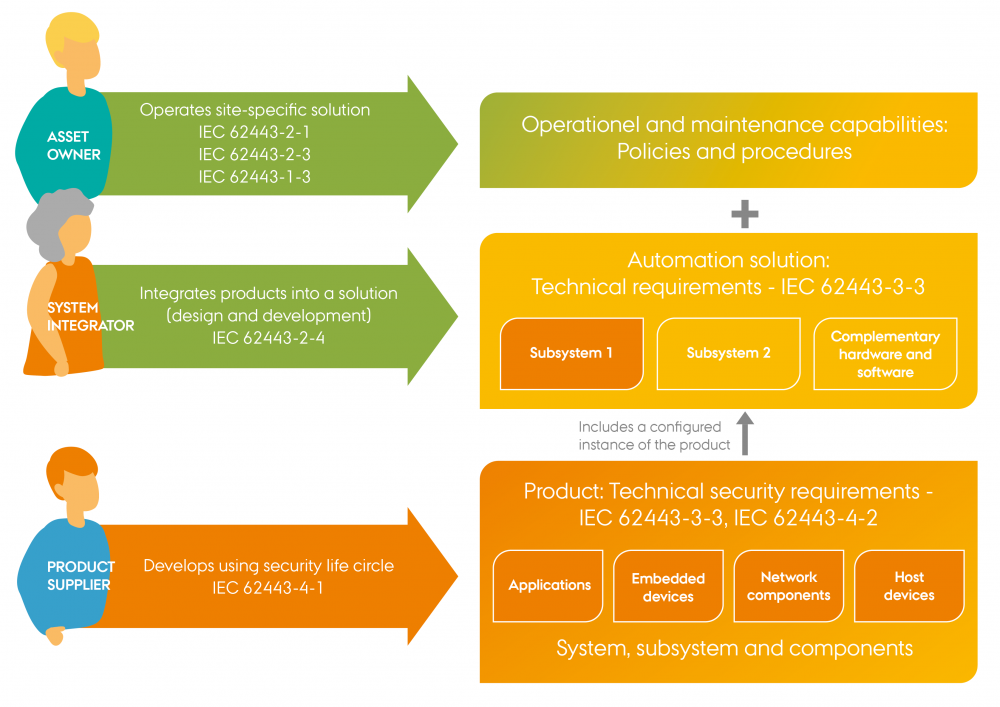
"The interplay between the IEC 62443-standards" by CyPro under license CC BY-SA 4.0
In the following, we will only explore the two standards IEC 62443-4-1, which includes design and maintenance processes, and IEC 62443-4-2, which specifies functional security requirements. For comparison, the functional requirements are not very different from ETSI EN 303 645. The major difference is seen in the processes that must be implemented for the development and maintenance of the products. The approach is to address security from multiple perspectives by developing a defence in depth strategy for the relevant products, as illustrated below.
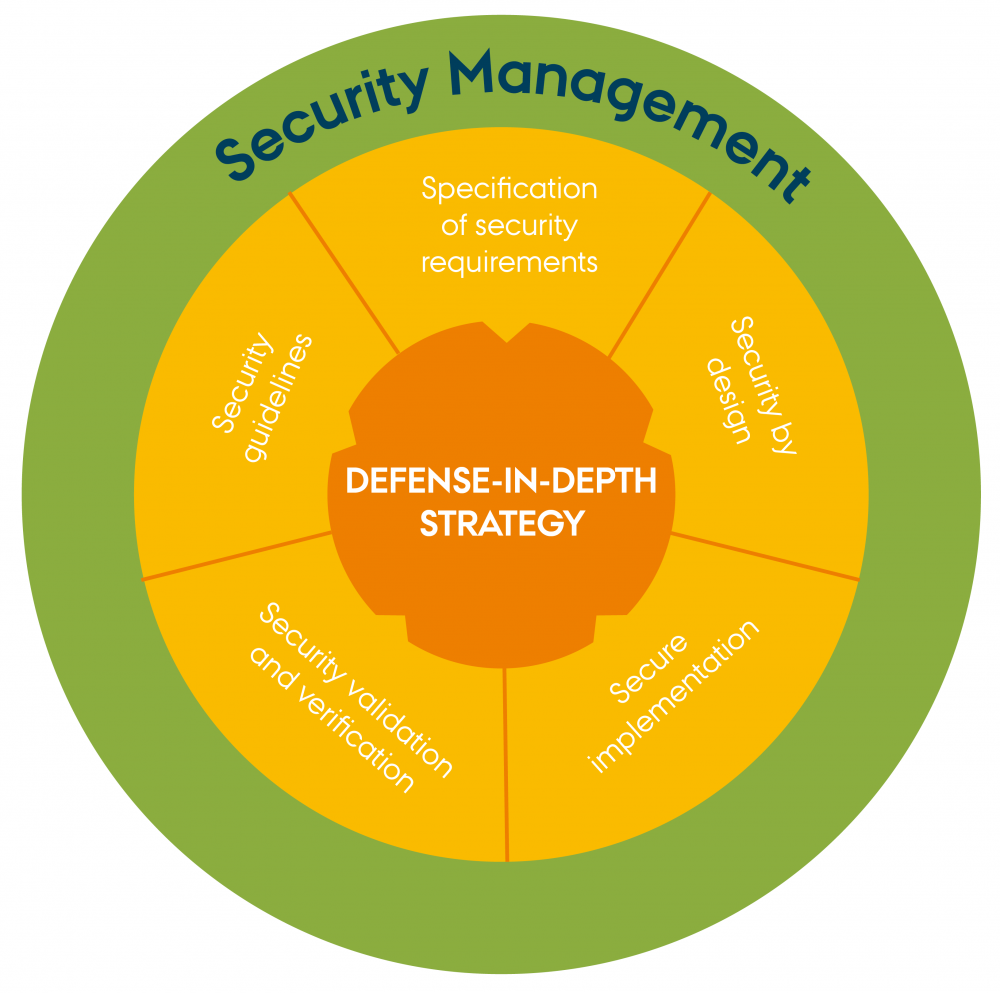
"Defense-in-depth-strategy" by CyPro under license CC BY-SA 4.0
It is therefore essential to draw upon multiple disciplines within product development to ensure a multi-faceted approach to the design. For example, one must be able to document the developers' competencies, the requirement specification for security functions, the process for software updates, etc.
The documentation and artifacts produced by following the processes defined in IEC 62443-4-1 will form the basis for a conformity assessment.
Expert advice
Standards can be a powerful tool, but like any other tool, they must be used correctly. A standard can certainly be applied outside its intended scope, but you must be aware of the potential issues this may cause, and it is important to be aware of the differences between the scopes. It is therefore perfectly acceptable to use, for example, EN 303 645 on an industrial product, provided you consider the changed threat landscape and ensure that the implementations and measures to be taken are appropriate for the application.
Output
This is a highly condensed summary of an immense and complex topic. An abundance of knowledge forms the basis for the standards that are being published, and they can have different impacts depending on the area to which they apply. This brief insight is intended to provide a general understanding of how these standards function and what to look for when you want to apply standards for IoT cybersecurity.
Next step
The next step will be to read one of the two standards presented in this module. Consider whether you fall within the scope of the standard you start with. Generally, a good starting point is to read ETSI EN 303 645. It sets a basic level that everyone should be able to reach, and on top of that, it can be downloaded for free.

The contents described above have been developed in the project:
’CyPro – Cybersecure manufacturing in Denmark’ by Aarhus University, Alexandra Institut, DAMRC, UGLA Insights and FORCE Technology funded by The Danish Industry Foundation. Material from the project is published under Creative Commons.
CyPro
You have completed the entire building block
Get your certificate for this completed building block. Request the certificate and we will send you the personal certificate.



