
February 28, 2025
Before you start
This learning module is part of the building block:
The module – in brief
The purpose of this module is to learn about the company’s IoT cybersecurity maturity.
The overall benefit of the tool is the collaborative dialogue and shared insights that become a common and explicit stepping-stone for further development and discussion of IoT cybersecurity across functions and stakeholders in the company.
The module is based on the situational analysis of each of the four building blocks. If you need a recap on the four building blocks, please consult The building block reference sheet.
The maturity dialogue is a way to take a step back and interpret and further discuss what the situation means.
The maturity dialogue sharpens the situational analysis, underlines the general tendencies in the company’s IoT cybersecurity, and prepares the company for working with their IoT cybersecurity based on a shared understanding.
Maturity concept
Building block maturity
The maturity concept is based on maturity for each building block. This means that each building block has its own maturity phase depending on how the company works with the tasks related to each building block.
One building block may be more or less mature than the other building blocks or be on the same maturity level.
The point is to avoid applying a general maturity phase to the entire company, which ultimately fits no one. Instead, the focus should remain on the actual IoT cybersecurity work being done by the company within the four building blocks.
The maturity model in itself has three phases. This means that each building block can be in one of the three phases.

"Maturity model" by CyPro under license CC BY-SA 4.0
The phased are named:
- Shared awareness of IoT cybersecurity
- Shared practice for working with IoT cybersecurity
- Shared structure for working with IoT cybersecurity
Each phase begins with the word shared. This recurring prefix denotes that the success criteria for each phase is to obtain an agreed upon and shared way of working with IoT cybersecurity in that phase, e.g. a shared practice for working with the quality of IoT cybersecurity for the company’s IoT solutions.
The phases are detailed in the work sheets made for the maturity dialogue.
Also note that:
- the maturity model illustrates that the early phase of maturity is more ‘up in the air’ than the structured phase, where a solid foundation for IoT cybersecurity has been established.
- there is a soft delimitation of the phases, shown by a colour gradient.
- you may have to revert to an earlier stage in a building block’s maturity to maintain the wanted level of IoT cybersecurity in the company.
Benefits of tool
The maturity dialogue anchors the situational analysis in a broader understanding of the trajectories of IoT cybersecurity development in the company and provides sighting lines into the future of the company’s IoT cybersecurity. At the same time, the tool helps to establish a shared language about IoT cybersecurity in the company.
The Maturity Dialogue tool
The maturity tool is presented in this video that describes both the phases and how to work with the maturity dialogue tool.
"Content of maturity dialogue" by CyPro under license CC BY-NC-ND
The maturity model is based on 35 interviews with Danish production companies about IoT cybersecurity.
The aim of the tool is for the participating people to 1) recognise and agree upon the maturity of each of the four building blocks in the company, 2) to have a collaborative dialogue about the IoT cybersecurity work being done in each building block, and 3) to use the shared insights into building block maturity to choose the next steps for the company’s IoT-cybersecurity.
Elements in the maturity dialogue
To help discussing the three maturity phases for each building block, we have made two sets of tool sheets for the company’s shared maturity dialogue.
- A set of keyword sheets providing an overview of the maturity progression for each building block in each of the three phases.
- A set of reference sheets providing more details about of the maturity of each building block in each phase.
![]()
Keywords sheet for all 4 building blocks
Printable version of the tool in large format
The example below shows the keyword sheet for the Organisational building block covering the three maturity phases: shared awareness, shared practice and shared structure.
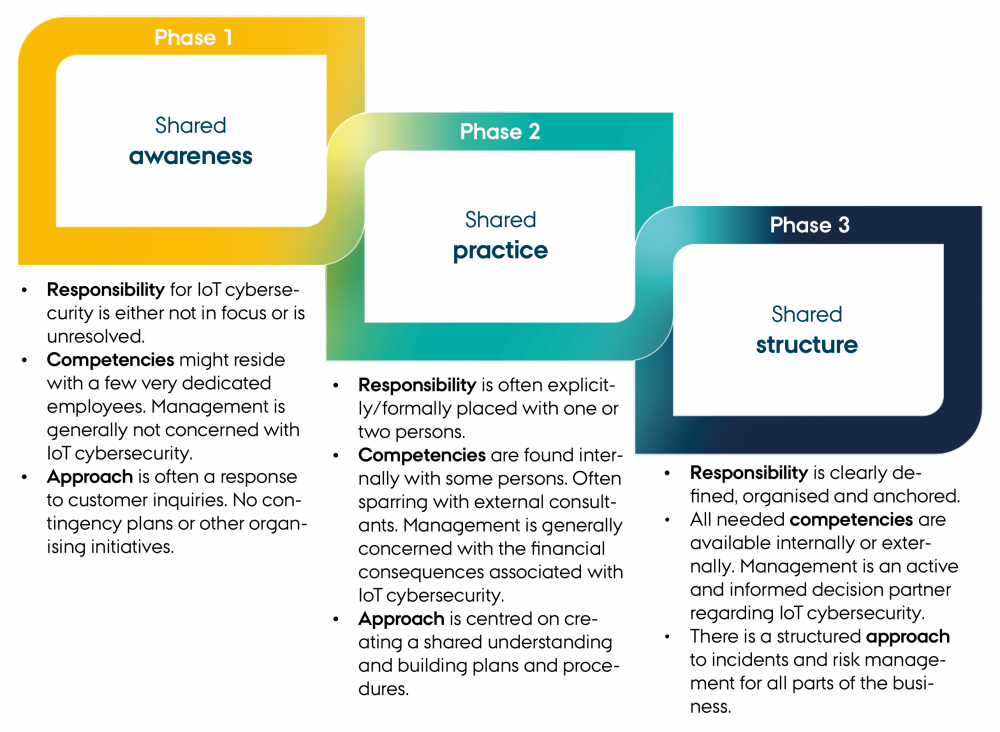
"Keywords sheet for the Organisational building block" by CyPro under license CC BY-SA 4.0
Each phase of the Organisational building block is described by the same three keywords: responsibility, competencies, and approach to IoT cybersecurity. The progression of the Organisational building block in the maturity phases is shown as changes in responsibility, competencies, and approach respectively. Each building block has its own keywords describing the building block's progression through the three maturity phases.
Just as in the setup of the keyword sheets, the reference sheet also describes the maturity progression in the organisational tasks for IoT cybersecurity, however, in greater detail across the three phases. The reference sheets can sustain the recognition of the phase of a building block as more examples and context are provided.
![]()
Reference sheet for all 4 building blocks
Printable version of the tool in large format
Practical information
The learning is conducted in a collaborative dialogue, ideally combining company representatives from all four building blocks for IoT-cybersecurity: e.g. employees and managers responsible for technical, quality, business and organisational tasks related to IoT-cybersecurity.
Other company stakeholders such as selected board members could also participate.
It doesn’t matter which building block you start with in the maturity dialogue – as long as all building blocks are covered.
It has proven useful to print out at least the keywords sheets and spread them on the table as the dialogue often jumps back and forth between building blocks, comparing their maturity progress in the flow of the dialogue.
There is no ambition of scoring the maturity for each building block or otherwise quantifying its progression.
Step-by-step guide
How to perform the maturity dialogue for IoT cybersecurity using this customised model is shown in this video.
"Instructions for maturity dialogue" by CyPro under license CC BY-NC-ND
The maturity dialogue includes the following steps:
- Invite the participants from the situational analysis, and make sure you have representatives from the company covering all four building blocks around the table. This meeting could be 1 hour long.
- Send a link to this online tool to the participants to help them prepare for the meeting.
- Print out 2-3 sets of keyword and reference sheets and bundle them by building blocks.
- At the meeting follow this agenda:
- Make it clear that it is about maturity for each building block, making it possible for each function working on that building block to assess its maturity independently of the other building blocks if needed.
- Revisit the situational analysis – to recap what you talked about last time and to get any new participants up to speed.
- Spread out keyword sheets (and reference sheets if needed) for each building block on the table.
- Ask someone working with the first building block from the left to describe its maturity.
- Afterwards everyone around the table may ask questions or add to the initial maturity statement.
- Agree upon a maturity phase for the building block and note it on the keyword sheet.
- Proceed through all four building blocks, double-back whenever it is needed to recapture or revisit a building block earlier discussed.
- Conclusion:
- What building blocks have an appropriate maturity considering your business and what you use IoT solutions for in the company?
- What building blocks have an appropriate maturity considering your business and what you use IoT solutions for in the company?
- Next step: decide on the learning path for the Organisational building block:
- If you have most building blocks in the phase shared awareness of IoT cybersecurity, it is recommended to proceed with the "Foundations track: Awareness" in the organisational building block.
- If you have most building blocks in the phases shared practice and shared structure it is recommended to take up the "Advanced track: Practice and Structure" in the organisational building block.
The best way to change your track through the organisational building block is to click on the link "go to organisation" in the green box at the end of the module, and then select either Foundations track or Advanced track, accordingly to your maturity dialogue.
If you press "Go to next module", you will continue on the track you chose from the beginning of the organisational building block.
Output
When you have completed the maturity dialogue, you have created a shared insight into the maturity of your work with IoT cybersecurity for each of the four building blocks in the company.
The insights can confirm which building blocks are already in good shape and highlight which to focus on to be able to handle the current and upcoming IoT cybersecurity risks and demands on your business, including demands from customers and legislation bodies.
The shared cross-functional dialogue creates a common perspective and also highlights the differences in working with and understanding the consequences of IoT cybersecurity in the company. The common perspective has the potential to become a shared frame of reference for cross-functional communication about IoT cybersecurity internally and externally, especially if the IoT cybersecurity responsible persons keep the insights from the maturity dialogue alive in discussions and communication.
Expert advice
It is easy to motivate people to participate in a maturity dialogue based on a simple, but empirically relevant maturity model. "Maturity model” is a well understood concept in both business, quality, organisational and technical settings.
Experience with the maturity dialogue with Danish production companies has shown that it is conceptually easy for company representatives to discuss and recognise their own company based on our worksheets, and that the dialogue sparks motivation and serves as a stepping-stone for the next IoT cybersecurity actions.
Next step
- Next step: decide on the learning path for the Organisational building block:
- If you have most building blocks in the phase of shared awareness of IoT cybersecurity, it is recommended to proceed with the awareness learning path in the organisational building block.
- If you have more building blocks in the phases of shared practice and structure it is recommended to proceed with the learning path of practice and structure in the organisational building block.
- If you have most building blocks in the phase of shared awareness of IoT cybersecurity, it is recommended to proceed with the awareness learning path in the organisational building block.
The best way to change your track through the organisational building block is to click on the link "go to organisation" in the green box at the end of the module, and then select either Foundations track or Advanced track, accordingly to your maturity dialogue.
If you press "Go to next module", you will continue on the track you chose from the beginning of the organisational building block.

The contents described above have been developed in the project:
’CyPro – Cybersecure manufacturing in Denmark’ by Aarhus University, Alexandra Institut, DAMRC, UGLA Insights and FORCE Technology funded by The Danish Industry Foundation. Material from the project is published under Creative Commons.
CyPro
You have completed the entire building block
Get your certificate for this completed building block. Request the certificate and we will send you the personal certificate.



