
May 30, 2023
Before you start
This learning module is part of the building block:
The module - in brief
The purpose of this module is to support a systematic dialogue on prioritising building blocks for IoT cyber security.
Key individuals from the company collectively assess the practical implications of the situational building block analyses and the maturity dialogue for the building blocks and prioritize the four building blocks based on their urgency for the company's business.
The result is a clear understanding of what is important here and now, and what will follow later. This is the basis for being able to make a relevant and a clear goal formulation for one building block for IoT cybersecurity.
Prerequisite for using the tool:
The company must have completed the work sheets linked to Situational analysis, and the Maturity dialogue tool for the building blocks.
Prioritising actions
Assessing how new knowledge and insights translate into practical actions can pose a challenge. One wants to utilise the new knowledge but doesn’t know where and how to start.
This video shows the two tools in the Foundations track. The first tool is the Prioritising building blocks tool, followed by the Goal formulation tool.
"Content and instructions for prioritisation and goals" by CyPro available under licensen CC BY-NC-ND
The prioritisation dialogue provides a structured reflection process that serves as a starting point for acting based on the knowledge about the company’s IoT cybersecurity. It focuses on determining the sequence of actions, rather than excluding actions.
Prioritising building blocks for IoT cybersecurity
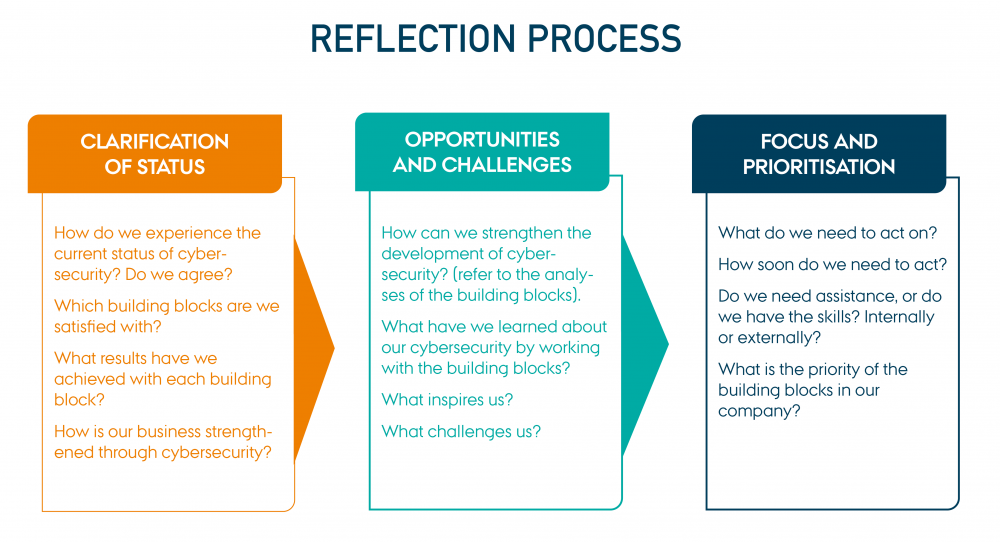
The prioritisation tool is a simple dialogue guide with three types of questions:
The purpose of the dialogue includes is to guide the company in prioritising a specific building block for IoT cybersecurity, which represents the cyber security task that needs to be addressed first.
The three types of questions cover the following topics across all four building blocks:
- the company’s perspectives on the current IoT cybersecurity status, and the reasons behind it.
- the company’s opportunities and challenges in further developing IoT cybersecurity.
- the company’s prioritisation of the upcoming IoT cybersecurity tasks by focusing on one building block for now.
Structuring the dialogue about prioritisation
It may seem cumbersome, but it is very important to stick to the structure of the dialogue.
The purpose of the dialogue's structure is to sustain reflection on the previous analysis of the current status of IoT cybersecurity before the company begins to act to further develop cybersecurity.
The reflection process built into the dialogue includes the following three steps where participants move from one perspective on the current status of cybersecurity, to reflecting on the opportunities and challenges for further developing cybersecurity, and finally prioritising one building block for over the threemothers.
“Reflection Process” from CyPro under licens CC BY-SA 4.0
Reflection process
Printable version of the tool in large format
Practical information
- Invite employees and managers who have participated in the previous analyses of the building blocks and who have decision-making power and knowledge of IoT cybersecurity.
- It is beneficial if knowledge about all four building blocks is represented at the meeting.
- Schedule a meeting with a duration of approx. 1 hour for the prioritisation dialogue.
- Provide each participant with a paper ‘kit’ of the company’s completed analyses sheets (situational analyses and maybe notes from the maturity dialogue).
- A manager/the meeting organiser prepares a brief oral summary of the previous analyses as an introduction to the dialogue.
Step by step guide
1) Present the prepared summary of the previous analyses of the building blocks (5 minutes).
2) Start by discussing the questions under Clarification of status - it is not necessary to take notes (15 minutes). Begin with the question: how do we experience the current status of cybersecurity in the company?
3) Proceed to Opportunities and challenges. During your discussion, you can elaborate on the insights from the clarification of status. It is not necessary to take notes (15 minutes).
4) Finally, the participants go through all the questions in the column Focus and prioritisation (20 minutes).
a) For the last question (what is the priority of the building blocks?), place a paper copy of each of the four situational completed analyses of the building blocks on the meeting table. Dedicate the rest of the meeting to prioritise them, where no. 1 is the most important building block for IoT cybersecurity in the company right now.
b) It should be done as a collaborative physical prioritisation of the completed sheets from the analyses of the building blocks. It can be beneficial if the participants stand up around the table.
5) Write down the sequence of the building blocks for cyber security and send them to the participants as a summary of the dialogue.
Outcome
Based on the prioritisation dialogue, you now have a clear picture of the significance and impact of the building blocks in your company. The dialogue prepares you to act on IoT cybersecurity through your own interpretation of what the building blocks mean in your specific context.
Additionally, the dialogue also facilitates internal knowledge sharing and contributes to establishing a common language for cyber security.
Based on the collective prioritisation, you now need to formulate a goal for the prioritised building block to ensure that the upcoming actions are clear and well-defined for everyone in the company.
Expert advice
Instead of perceiving cybersecurity development as a task to be carried out by a single individual, having a common language and consensus about prioritised cybersecurity actions increases the company’s awareness of IoT cybersecurity and strengthens discussions.
It is important to realise that specific goals for the next steps can only be defined, once the building blocks have been prioritised. This enables the cybersecurity team to make concrete and inspiring goals based on tangible content.
Next step
The next step is to define a specific action and an expected goal for the action – both related to the building block with the highest priority. The tool Goal formulation can be used.

The contents described above have been developed in the project:
’CyPro – Cybersecure manufacturing in Denmark’ by Aarhus University, Alexandra Institut, DAMRC, UGLA Insights and FORCE Technology funded by The Danish Industry Foundation. Material from the project is published under Creative Commons.
CyPro
You have completed the entire building block
Get your certificate for this completed building block. Request the certificate and we will send you the personal certificate.



