
March 28, 2025
Before you start
This learning module is part of the building block:
The module in brief
Threat identification is critical in the risk management process that focuses on uncovering potential threats to an organsation's systems, data, and operations. This module introduces a systematic approach to identifying threats, ensuring that no major weaknesses are overlooked.
Purpose of threat identification
Through structured discussions and practical tools, this module helps establish a list of threats, forming the foundation for subsequent risk analysis and mitigation planning. By understanding threats and their potential impact, organsations can better prioritise their efforts and safeguard their systems and operations against cyberattacks.
Practical information
As with system modelling, it is recommended to involve a diverse range of participants in the process, including management and technical profiles. Building on the foundation established in system modelling, we use the flow diagram of the system and system documentation as a base for threat identification.
A threat identification session is often conducted as a workshop, possibly supported by purpose-made tools. If you do not intend to use any special tools, you will need a whiteboard/flipboard, coloured markers, post-its, pens, and printed copies of the downloaded tools.
Allocate at least 1 to 2 hours for the threat identification process, though the total duration may vary depending on the complexity of the system being assessed.
Step-by-step guide
Threat identification involves the following steps:
Step 1:
The first crucial task is to determine where threats could occur within the system. This involves identifying points where data crosses trust boundaries and where interactions between components or users could introduce vulnerabilities. Use the system model obtained in the previous system modelling module. These areas present higher risks as they are the areas most likely to be subject of an attack.
Step 2 (optional):
Also consider insider threats by examining data exchanges within trust boundaries. This can uncover potential internal threats but may also reveal incorrect trust assumptions. This can expose risks, such as malicious insiders, accidental misconfigurations, or compromised internal systems.
Step 3:
After determining high-risk areas, the concrete threats affecting these areas need to be identified, classified and evaluated, which requires structured methods. Three key methods to identify, classify and evaluate concrete threats include:
-
- applying the CIA Triad to identify threats to confidentiality, integrity, and availability
- applying STRIDE to identify threats based on spoofing, tampering, repudiation, information disclosure, denial of service, and elevation of privileges.
- leveraging threat catalogues such as MITRE ATT&CK or CyPro Threat Catalogue (shared below) to identify common threats.
Depending on the system complexity and risk priorities, organisations can use one or combine multiple methods based on their specific context, goals, and available resources. The three methods are introduced in the following sections.
After having performed the threat identification step-by-step, the organisation should have a list of potential threats that need to be further analysed. You may find a practical example to see how the threat identification process is applied in a real-world scenario, below the introduction to the three methods.
CIA triad
This method focuses on identifying threats that would violate the Confidentiality, Integrity, and Availability (CIA) of one or more assets, the three core pillars of information security. Organsations can use this method to evaluate how threats impact data flows across trust boundaries. The output of this method is a classification of violation types, helping organsations prioritise security measures where breaches could lead to data leaks, unauthorised modifications, or service disruptions. It is particularly useful for systems with well-defined data flows, allowing organsations to pinpoint high-risk trust boundary crossings where violations are most likely to occur.
Confidentiality violation – Occurs when unauthorised individuals gain access to sensitive data. Examples include eavesdropping on communication between an IoT gateway and cloud service, radio communication between an IoT sensor and an IoT Gateway, data breaches, or exposure of confidential information across trust boundaries. Attackers exploiting weak encryption or misconfigured access controls could intercept credentials, or operational logs, leading to compromised security.
Integrity violation – Happens when an attacker modifies data or system components without authorisation. This includes tampering with transmitted data flows, injecting malicious commands, or manipulating system logs to cover unauthorised activities. For example, an attacker intercepting and altering command messages between an IoT gateway and mobile application could cause unauthorised behaviour in the IoT system, leading to severe security breaches.
Availability violation – Results from disruptions that prevent legitimate users from accessing or controlling system functions, often within critical time boundaries. Common threats include denial-of-service (DoS) attacks, resource exhaustion, or system failures, which can have severe consequences depending on the duration of the disruption. Availability threats are especially critical when they extend beyond acceptable time limits, leading to service downtime, operational failures, or safety risks. For instance, an attacker targeting an IoT gateway with a DoS attack could temporarily block remote control of the IoT system, but if the disruption persists beyond an acceptable timeframe, it could escalate into a major system failure.
The results of the CIA Triad analysis can be documented in a structured table, as shown below. This table helps categorise identified threats, map them to their respective violation types (Confidentiality, Integrity, Availability), and provide a clear description of their impact on the system. The insights generated here are further analysed in the threat analysis.
![]()
Mapping threats to CIA violations
Printable version of the tool in large format
![]()
Threat modelling
Printable version of the tool in large format
STRIDE framework
The STRIDE framework offers six categories of threats: Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege. By using STRIDE, companies can systematically assess if one or more of these threats are applicable to each component/interaction of their system. The insights generated here are further analysed in the threat analysis module . This method is ideal for organsations looking for a structured way to analyse specific types of attacks. It works best when companies want to go beyond high-level threats and identify detailed, technical risks associated with individual system elements. The six categories of threats include:
- Spoofing – Identify if there are threats where an attacker could impersonate a legitimate user or system component. This includes unauthorised access through stolen credentials or fake identities.
- Tampering – Assess if there are threats where attackers could modify data or system components. This includes altering messages, injecting malicious code, or manipulating transmitted information.
- Repudiation – Determine if there is a risk, where users or systems can deny actions, they have performed. This could be due to lack of audit logs, non-repudiation mechanisms (e.g. signatures), or insufficient tracking of transactions.
- Information disclosure – Identify if there are threats related to unauthorised exposure of sensitive data. This includes unencrypted communications, misconfigured access controls, or unintended data leaks.
- Denial of Service – Evaluate if there are threats that could impact system availability. This includes resource exhaustion, overwhelming system requests, or targeted service disruptions.
- Elevation of privileges – Assess if there are vulnerabilities that could allow attackers to gain unauthorised higher-level access. This includes exploiting weak permissions, privilege escalation, or bypassing authentication mechanisms.
Threat catalogue
Threat catalogues provide a library of pre-defined threats, offering organsations a structured way to identify common vulnerabilities. A well-known example is the MITRE ATT&CK framework, which provides an extensive and detailed collection of real-world attack techniques. The insights generated here are further analysed in the threat analysis module. However, MITRE ATT&CK can quickly become complex and overwhelming, especially for organsations new to threat modelling. To simplify this process, we have developed the CyPro Threat Catalogue, which offers a business-friendly and IoT-specific approach, making it easier for companies to identify and assess threats relevant to their system.
![]()
List of 50 potential threats pertinent to an IoT door lock system
Printable version of the tool in large format
IoT door lock example
To analyse the IoT door lock system, we follow a structured approach to identify threats using the step-by-step method outlined earlier and categorise them based on Confidentiality, Integrity, and Availability (CIA) violations. This allow us to systematically assess threats across different components and trust boundaries, ensuring that potential confidentiality breaches, integrity compromises, and availability disruptions were identified and addressed effectively.
Step 1:
We first analyse data flows crossing trust boundaries, as these represent high-risk areas where unauthorised access, data tampering, or disruptions could occur. The trust boundary, as shown in the diagram, encompasses the IoT door lock and IoT gateway. This means that interactions within this zone are trusted (as we only consider attackers with remote access in this threat identification). Exchanges beyond the trust boundary (e.g., with cloud services and applications) may introduce potential security threats.
Key data exchanges across trust boundaries include:
-
- IoT gateway ↔ Cloud service: Remote communication for data storage, processing, and command execution.
- IoT gateway ↔ Mobile application – Secure transmission of user authentication requests, access control commands, and status updates between the gateway and mobile device, where an attacker could intercept or manipulate data.
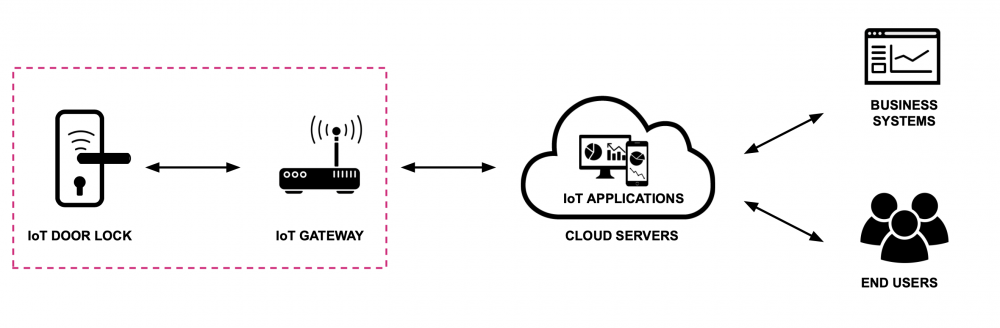
Illustration: Key enabling technologies for IoT door lock solution
Step 2:
Next, we consider data flows within the defined trust boundary (IoT door lock and IoT gateway) to ensure that no internal vulnerabilities were overlooked. As communication is wireless, it is subject for a number of threats, e.g. eavesdropping and jamming. However, these threats are all introduced by individuals with physical proximity/access to the system, such as employees, maintenance personnel, or attackers being near the physical lock.
Key internal threats include:
-
- IoT door lock ↔ IoT gateway: Potential unauthorised firmware updates or tampering with lock status.
- Physical access to the lock – Attackers could manipulate hardware components, intercept local signals, or attempt brute-force unlocking.
Step 3:
After determining where threats could occur, the next step is to identify and categorise specific threats using structured threat modelling methods. Applying the CIA Triad, we categorise the identified threats based on violation types, considering security risks arising from trust boundary crossings and internal vulnerabilities.
Confidentiality violation – Unauthorised access to communication between the IoT gateway and cloud service could expose sensitive data, such as user credentials, lock control commands, and operational logs. An attacker intercepting these transmissions could compromise all connected devices, leading to data leaks, unauthorised access, and potential remote-control takeovers. Similarly, weak authentication within the trust boundary could allow insider threats to gain access to confidential system configurations.
Integrity violation – Attackers could tamper with commands or data transmitted between the IoT gateway and Mobile Application, resulting in unauthorised unlocking of doors or modification of access permissions. Exploiting weak API security or injecting malicious payloads could allow attackers to manipulate system behaviour, potentially corrupting security logs or overriding legitimate access controls. Additionally, physical access to the IoT door lock or Gateway could allow attackers to install malicious firmware or manipulate local system states.
Availability violation – A denial-of-service (DoS) attack on the IoT gateway or cloud service could disrupt remote access, preventing users from unlocking or controlling their devices when needed. Attackers could exploit service outages to block legitimate users from entering facilities, disable critical security controls, or cause widespread operational disruptions. Wireless communication is also susceptible to jamming attacks, where an attacker physically near the device could interfere with communication, leading to temporary or prolonged unavailability of the system.
The table below summarises the direct output of this process, where each interaction and component were evaluated against the CIA Triad to identify potential threats.
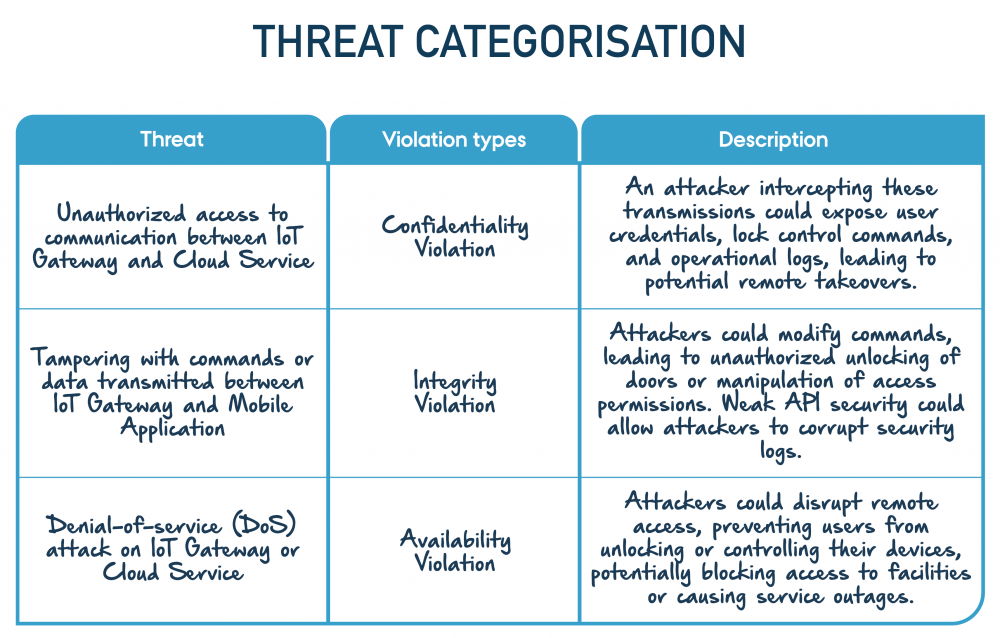
Example on how to fill out "Mapping security violations to CIA principles"
Output
By applying one or a combination of these methods, organsations can systematically identify and categorize threats. After having performed the Threat Identification, the organisation should have a list of potential threats, along with the assets the threat could affect and how. This list is further analysed in the subsequent module through a threat analysis.
Expert advice
Various guidelines and catalogues exist for supporting the threat identification process. Below are some threat catalogues that provide more details about potential threats.
ISO 27001 & ISO 22301 Knowledge base – Catalogue of threats and vulnerabilities
BSI IT-Grundschutz Threat Catalogues
Next step
The threat identification offers a comprehensive list of potential threats to the system, that can be further analysed in the next module Threat analysis.

The contents described above have been developed in the project:
’CyPro – Cybersecure manufacturing in Denmark’ by Aarhus University, Alexandra Institut, DAMRC, UGLA Insights and FORCE Technology funded by The Danish Industry Foundation. Material from the project is published under licence CC BY-SA 4.0
You have completed the entire building block
Get your certificate for this completed building block. Request the certificate and we will send you the personal certificate.



